Okay, listen up. I gotta share this practice I ran last week. You know how sometimes you’re stuck in a mess where someone is just being deliberately tricky, right? I was neck-deep in this contract situation, dealing with a partner company that was supposed to be supplying us with some critical hardware schematics for a rollout we were managing. My main contact, let’s call him ‘Gary,’ kept promising specific delivery dates, swearing up and down he’d have the specs finalized and approved by Tuesday morning. Tuesday rolled around, then Wednesday, then a whole week went by, and nothing official showed up in our shared documentation portal. Dead silence.
Then I hear through the grapevine—you know how these things go, a casual lunch with a guy who knows a guy—that Gary didn’t miss the deadline because of internal delays. He actually went straight to my lead engineer and started subtly trying to change the required input voltages for the entire system. He was trying to sneak in cheaper components on his end, effectively forcing us to rewrite our integration documentation and shoulder the cost of the last-minute change. Classic, manipulative sleaze move designed to save his butt and cost us serious overhead. I felt the heat rising instantly.
Pulling the Practical Advice
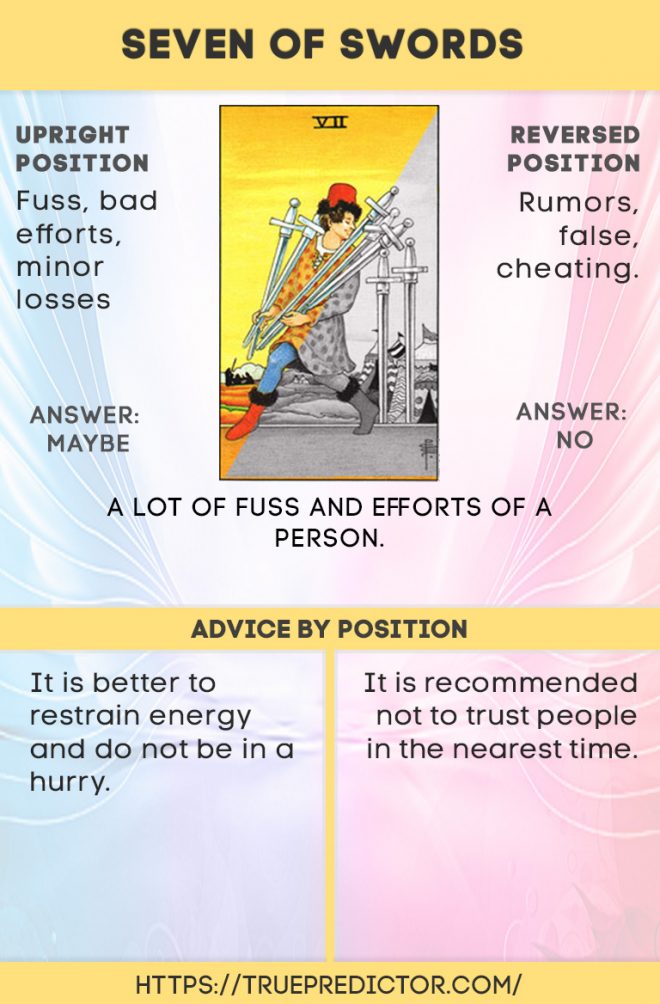
I sat there fuming. My first instinct, the gut reaction, was the worst one: call him out, scream about breach of contract, and threaten to shut the whole operation down immediately. But I stopped myself. I figured, let’s check the compass. I always pull a card when I hit one of these confusing roadblocks where emotion tries to override logic. I shuffle the deck a few times, asking, “What is the smartest action to take right now, given this clear deception?” I cut the deck, and bam—the Seven of Swords pops right out, plain as day. The guy sneaking away with five swords, leaving two behind.
It was immediately clear what the energy was: someone is trying to steal something—credit, time, or advantage—by being underhanded. But the advice of the card is crucial: it’s not just about noticing the theft; it’s about how you respond to protect yourself. It tells you to be strategic, to avoid direct confrontation when you’re outmatched, and to retreat with whatever resources you can save. My initial plan, the screaming confrontation, was just leaving more swords for Gary to use against me, making me look erratic and unprofessional.
I needed to pivot immediately. I needed to act like I didn’t know what he was doing, while silently gathering irrefutable proof and securing my own position.
- I immediately started documenting every single conversation my team had had with Gary’s people, every unsigned email, every sketchy, verbal change request. I logged it all onto an external, secured server that he couldn’t touch.
- I pulled my lead engineer off the communication loop with Gary entirely, telling him we had to “refactor the staging environment” (which was code for isolating their work from Gary’s influence until we had a clear path).
- I stopped responding to Gary’s passive-aggressive, deadline-missing emails immediately. I let them sit. I bought critical time.
The realization hit me hard: the Seven of Swords wasn’t telling me to fight the thief; it was telling me to outmaneuver him. It was about quietly saving my work and proving his deception later, when he thought he had already gotten away clean. It was about being the smarter sneak, the one who saw the move coming and built a trap.
Why I Trust the Strategic Retreat
I learned this lesson the absolutely hardest way, years back, when I was trying to get my first business off the ground. I poured easily twelve months of my life into designing this specific software suite for small business management. I worked every weekend, skipping family events, blowing off friends. I was obsessed. I made the mistake of bringing on a co-founder who seemed like a good guy, great network, charming face. Turned out, he was all face and no spine.
After six months of collaboration, he took my core source code, changed the company name slightly, filed the trademark under his own personal holding company, and froze me out of the bank accounts. He smiled, told me I had done ‘great foundational work,’ and then used my own creation to kick me out the door. I was furious. I tried to argue, I tried to show the timestamps on the code commits, but he had legally shielded himself just enough to make a lawsuit prohibitively expensive for me, the guy suddenly with zero income. He got the product, and I got a mountain of debt and a profound education in human betrayal.
That incident wrecked me for years. It taught me that integrity means nothing when you are dealing with a motivated liar who thinks they are entitled to your hard work. I swore then and there I would never let myself be caught flat-footed again. If people are going to play dirty, you have to play smart. You have to build an impenetrable wall of evidence before they even realize you noticed they pulled out a shovel.
The Final Move and Implementation
So, back to Gary and the hardware schematics. After I had secured my team’s code and compiled all the documentation of his sneaky moves, I waited until Friday afternoon. I had all the proof of his unauthorized scope manipulation laid out chronologically. I didn’t send it to him; that would just start a fight. I sent the entire package straight to his supervising project manager and the VP of Procurement, attaching a clear timeline showing exactly when he had asked for changes outside the official signed contract and change order process. I didn’t accuse him of stealing or lying. I just presented the facts.
My email stated, very clinically, that due to the conflicting instructions received from ‘Gary’ and the official scope document, we were forced to immediately pause all critical development work until the client clarified the actual requirements and issued a formal, paid change order reflecting the new demands.
Gary called me five minutes later, absolutely raging, threatening to terminate the contract and blacklist my company. I just stayed perfectly calm, repeating the same mantra: we need official paperwork to proceed, period. He tried to deny everything, backtrack, claim confusion, but the documented email trail was already sitting with his bosses. He tried to sneak away with the advantage, but I had blocked the exit.
What did I learn? The advice of the 7 of Swords isn’t always about being the thief. Sometimes, it’s advice to act like the thief’s silent observer—to collect the evidence, retreat strategically without a fight, and make your definitive move when the sneak thinks he’s safe. It saved my contract, my team’s bandwidth, and frankly, a ton of money. Always document everything. Secure your resources first. Don’t fight; just move smarter than the opponent who thinks you’re distracted.